What is Cyber Security?
Cyber security is a growing field in the world of high technology. Given the rise of cyber-crime, government agencies and private firms alike have increased their efforts to build strong and effective cyber security teams. Government agencies, such as the National Security Agency and the Department of Homeland Security, have even teamed up to create a special accreditation for college cyber security programs. Other agencies, such as the CIA and FBI, have implemented internships and fellowship programs for cyber security students. These programs not only enhance students' education with experiential learning but graduates of these programs may find a job offer after successfully completing these programs. In any case, these internship participants have the opportunity gain a specialty area within the cyber security realm.
Generally speaking, cyber security professionals work to thwart hackers, dismantle malware, and protect databases of all sorts. To achieve these broad goals, cyber security professionals work as cryptographers, penetration testers, security architects, and security analysts. In any of these fields, information security teams conduct constant research to keep abreast of the latest tactics employed by black-hat hackers. They also need to audit any and every exposure their firm has to the wider internet. Malware downloads are likely to breach security and even dubious websites may load cookies that could track employees in ways that nobody wants.
Featured Online Programs
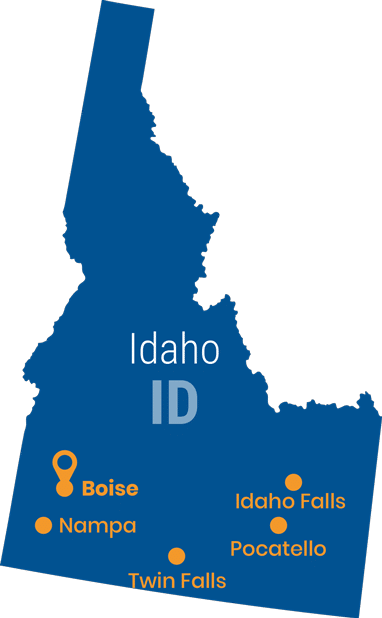
Online Cyber Security Education in Idaho
To address the needs of its government agencies and business communities, the state of Idaho has responded with cyber security degree programs. Once an Idaho student has a degree in cyber security, they can help to protect sensitive databases, such as the Idaho State Tax Commission's systems, which contain the social security numbers, income information, and other sensitive data points on the state's citizens. On top of this, the state's banks and other financial institutions must be protected from ransomware attacks and other black-hat activities.
A cyber security specialist is a high-tech professional who works to secure and maintain computer systems. These professionals are found performing any one of a number of tasks. Some are security architects who mastermind security systems, some are penetration testers who try to break into those systems, and still others specialize in cryptography and devising impenetrable virtual walls of code. Thus, these computer specialists work at computer terminals using a variety of operating systems, including MACOS, Linux, and Windows.
Cyber security specialists also work in a variety of environments. Most likely work in information technology departments, where they monitor the databases and networks. These workers may work from home but many report to an office for regular business hours. There are also cyber security professionals who work as consultants. Penetration testers most often fall into this category since they seek to emulate the bad-guy black hat hackers in their efforts to test security systems and security protocols. These consultants typically work from home, but they might also travel to meet their clients and may even work in their offices.
Online Associate (AS)
This level of cyber security education is a great way to get a leg-up into the field of cyber security. Many community colleges are adding cyber security or information security courses and majors to their curricula. Of these, several carry top credentials as Centers of Academic Excellence, an accreditation given by the National Security Agency and Department of Homeland Security.
While many employers may prefer a bachelor's cyber security degree, an associate cyber security degree is also acceptable for an entry-level position. Cyber security professionals who work with a two-year degree can improve their credentials with certifications form professional agencies that will bolster their resumes. For instance, some pursue InfoSec credentials specifically, but others may choose to sharpen other, more general skills such as coding languages, database administration skills, and more. Nevertheless, a certificate in a security specific topic such as cryptography might be of more utility in the job market.
National Rankings - top 25 online associate ProgramsOnline Bachelors (BS)
Careers in information security typically take off with a bachelor's cyber security degree. This level of educational achievement indicates to employers that a worker has spent a great deal of time immersed in cyber security and that they have also earned a well-rounded education that will bolster their critical thinking skills. In fact, many cyber security students can expand their abilities with advanced coursework in mathematics, computer science, and even criminal justice.
Cyber security students should also seek to expand their resumes with internships, which many departments support. Not only does an internship provide real-world opportunities to apply learning but the experience can support a resume, especially when those experiences resulted in completed projects or other accomplishments.
A bachelor's cyber security degree is not only a great support for landing an entry-level job, but it is a necessary step towards enrolling in a graduate cyber security degree program. Some may even find accelerated master's degree programs that allow students to complete both a bachelor's and master's cyber security degree in a mere five years.
National Rankings - top 25 online bachelors ProgramsOnline Masters (MS)
A master's cyber security degree is becoming more and more vital to long-term success in the field of information security. This is because the cyber-criminals are becoming ever more skilled and clever, so the more in-depth study and work a professional can do the better.
A master's cyber security degree offers professionals the opportunity to focus their studies to specific areas within the field of cyber security. Some may want to focus their research on cryptography and others might prefer to work on subjects like networks or database security. There are still others who have their eyes on the C-suites and upper-level management. Those professionals will need an MBA with a cyber security concentration.
An MBA may seem like a divergence from information technology and cyber security, but the degree will only broaden skills and abilities to include business administration. Then the second year of an MBA can concentrate on cyber security, provided the program supports this. On the other hand, cyber security professionals may choose a dual MBA program.
A dual MBA degree program allows students to work on both an MBA and a computer science or information technology master's degree simultaneously. These programs take only three years to complete both degrees and create graduates who are a double threat in the job market. That is, they will be business administration experts on top of their cyber security acumen. Before long, these graduates can hold titles such as CIO and CSO.
National Rankings - top 25 online masters ProgramsOnline Doctorate (PhD)
Technology is advancing at such a rapid pace that cyber security professionals increasingly need more education to keep up. Cyber criminals are advancing their knowledge at a rapid pace and any advanced study into cyber security and cryptography can be of immense utility in the field. In fact, some employers hire PhDs to conduct research so that they can develop tighter security for their firm and possibly create new cyber security products to sell on the market.
However, the larger need for doctorate degrees in this field is in the classroom. Those with this level of academic achievement can apply their skills in the classroom to teach the next generation of tech specialists. With a PhD, a professional can teach at the undergraduate or graduate school level. Their doctorate can also help them land a tenure track position that entails long-term job security and a healthy salary.
UniversityHQ resources and scholarships guide for computer science Check out the FAFSA and financial aid guideGet Matched With Cyber Security Colleges
Become a Cyber Security Professional in Idaho
It's not easy to become a cyber security professional in Idaho, or anywhere, for that matter. The field is very demanding, and professionals need to spend a lot of time in deep study and research to become proficient. After all Idaho's banks, government agencies, and other organizations will be trusting their vital databases and networks to any cyber security professional they hire. Further, the field requires that information security professionals be part computer science whiz and part criminal justice sleuth.
These skills and attributes are developed early in life. Youngsters who are drawn to figure out how websites and mobile devices work are obvious candidates for any high technology field. When they also are prone to investigate suspicious activity online, they may be priming themselves for a career in cyber security. They might exhibit a natural propensity for critical thinking and don't accept information at face value. When friends try to pass along misinformed articles or information, they are likely to dive deeper to debunk or affirm the information before accepting it.
Future cyber security professionals in Idaho may start their academic journey toward the profession while still in high school. They may be lucky enough to have access to a school that offers courses in computer coding or information technology topics. Barring that, many high technology experts started out teaching themselves coding languages and even earning certifications online to prove their knowledge. Even schools that don't have a full computer science curriculum may support students with a computer club. These informal organizations can be stimulating and have encouraged many to work together to create fun games or other bits of software. This experience will pay off later when they are digging through code to discover weaknesses in a firewall, for instance.
Finally, cyber security professionals need to earn a bachelor's cyber security degree if not a master's information security degree. They should seek out the best-accredited program possible. A baseline for a search is a regional accreditation. However, students will be best served by an accreditation from ABET or a cyber security program that is designated as a Center of Academic Excellence (CAE) by the NSA and the Department of Homeland Security.
See top 50 affordable cybersecurity schools and universitiesCareers for Cyber Security Graduates
- Security Analyst
Cyber security analysts are information security professionals who analyze computer security systems to ensure that they meet high standards for the industry. Analysts may also be proactive in implementing new technology solutions and security protocols for their firm or client. Security analysts not only dive deep into the code that protects their firm's cyber assets, but they also work with employees to ensure that everyone understands how to create the most secure passwords and how to not be duped by people wishing to trick them into releasing sensitive information. - Information Technology Manager:
After several years in the IT field, professionals might move up into management of their IT department. These professionals are in charge of seeing that everyone is on task and that large projects are executed with efficiency. IT managers may also be in charge of things like hiring, firing, payroll budgets, technology budgets, and communicating with other managers in the firm. IT managers often earn an MBA and then progress higher, perhaps reaching the C-suites. - Network Administrator:
These information technology experts are in charge of overseeing their firm's networks. They are trained in networking by an information technology degree program, and many earn special certifications in the technology their firm uses. For instance, some may earn a certificate in Cisco Systems, Microsoft networks, or other technologies. - Cloud Information Security Engineer:
Firms are increasingly using cloud computing systems for their database and other needs. These IT experts are fully educated as to how to secure a cloud file server. They may work with Amazon's technologies or some other solution products. - Penetration Tester:
These cyber security professionals often have years of experience in information security on top of graduate degrees and industry certifications. Their job is to try to hack into a system and report on the weaknesses they found. Thus, penetration testers are often called white hat hackers. - Information Security Analyst:
These cyber security professionals are charged with building and maintaining security systems and protocols for their firm. Information security analysts are typically trained in cyber security and hold a bachelor's degree from an accredited college or university. Their jobs may entail finding new software solutions or creating new cyber security protocols for employees at their firm. - Chief Information Security Officer (CISO):
This is the ultimate position for any cyber security professional. CISOs typically have a lot of experience in information security on top of a master's degree in cyber security or even an MBA, if not both. Their careers also include many certifications they earn that has enabled them to create a successful track record. - Security Architect:
These information security experts are trained to create wholly new security systems for their firm or client. They might work as outside consultants for firms that don't yet have their own cyber security solutions. Security architects also work to maintain information security systems. - Information Security Manager:
With multiple years of proven cyber security experience, a professional might move up into this position. Information security mangers oversee a team of security analysts and architects. They may hold graduate management degrees or master's cyber security degrees, if not both. From this level in the corporate hierarchy, information security managers can move into upper management, if not the C-suites and a position such as CISO.
More info about cybersecurity jobs & careers guide
Search All Programs
